Adversarial Domain Adaptation Learning for Accelerating Artificial Intelligence Based Military Solutions
Military / Coalition Issue
Training deep learning (DL) models requires large amounts of labeled data. Collecting and labeling data is often time-consuming, and thus unfeasible in applications with time constraints.
Core idea and Key Achievements
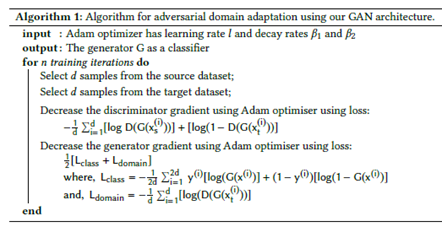
Our approach takes advantage of knowledge sharing in coalitions. We propose the use of Domain Adaptation (DA) to reduce the amount of labeled data required for training a DL models. DA is a transfer learning technique that allows one to transfer knowledge from a source domain with adequate training data, to a different but similar target domain with minimal or no new training data. We use a specific form of DA, referred to as adversarial DA, that GANs for creating a domain-invariant mapping of the source and target datasets. Our DA generative adversarial network (GAN) architecture consists of a generator and discriminator that are deep neural networks (DNNs) with the same layer configuration (see figure).
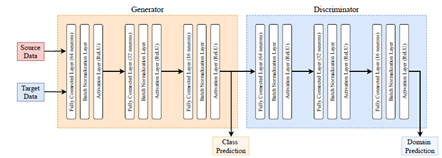
They both consist of 9 layers with 3 sets of fully connected layers, a batch normalization layer, and a reLU activation layer stacked on top of each other. The fully connected layers have 64, 32, 16 neurons in that order. The last layer of the generator serves as input to the discriminator as well as feeds into a soft-max layer to predict the class of the data sample. Similarly, the final layer of the discriminator feeds into a soft-max layer to predict the domain the sample belongs to. The algorithm is below.
We have tested our DA GAN approach for training DL models for intrusion detection for two different cases. The experiments show that our approach achieves higher accuracy than the base case (e.g., no TL is used) and a fine-tuning approach.
Implications for Defence
Our approach supports an approach to address the scarcity of training datasets.
Readiness and Alternative Defence Uses
Provides a technique that can be immediately engineered and applied. However, more experiments may be required to assess the suitability of the technique for a large variety of application domains and data.
Resources and References
- Singla, Ankush, Elisa Bertino, and Dinesh Verma. “Preparing network intrusion detection deep learning models with minimal data using adversarial domain adaptation.” In Proceedings of the 15th ACM Asia Conference on Computer and Communications Security, pp. 127-140. 2020.
Organisations
Purdue, IBM US