Data Plane-based Technique for Network Topology Inference
Military / Coalition Issue
Military coalition networks often suffer from sub-optimality caused by lack of a global view of the network state. Knowledge of the global network state (including topology and performance metrics) is the key to many network operations such as service placement and traffic engineering. Directly acquiring the network state of coalition partners in the control plane is subject to constraints by policies. A question of interest is: Can we develop a data plane-based technique to learn the state of coalition networks from measurements readily available at our own nodes?
Core idea and key achievements
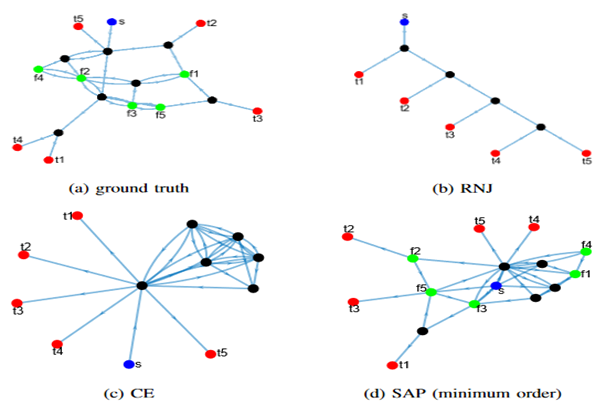
We address the above challenge by developing topology inference algorithms that infer the structure and state of a target network from end-to-end measurements at a subset of nodes, using techniques from network topology tomography. While existing algorithms are limited to trees or union of trees denoting routing topologies, our algorithms can:
- infer not only the routing topology but also the placement of in-network processing units (e.g., virtualized network functions),
- infer how each measurement path traverses the internal nodes/links and the network functions,
- guarantee consistent reconstruction of all the measurements while existing algorithms may fail under non-tree-based routing.
We use a novel two-step approach by first solving a possibly under-constrained linear system to infer the sum weight of links traversed by the same set of paths (called category weight), and then inferring a logical topology based on the category weights and the service chains. Our solution has guaranteed accuracy in several special cases and improved accuracy in the general case compared to state-of-the-art algorithms.
Implications for Defence
From the perspective of network management (e.g., network slice allocation), the proposed algorithms can provide a logical view of the coalition network state across coalition boundaries without requiring direct control plane access, thus facilitating easy deployment of services and migration of algorithms designed for single-domain networks. From the perspective of security and privacy, the proposed algorithms provide a view of what an adversary can infer from end-to-end measurements at a subset of compromised nodes, thus facilitating vulnerability analysis and design of defences (e.g., periodic updates of slice allocation as a moving target defence).
Readiness & alternative Defence uses
Besides algorithms, we developed experimental implementations code and case studies on real network topologies.
Resources and references
- Lin, Yilei, et al. “Looking glass of NFV: Inferring the structure and state of NFV network from external observations.” IEEE/ACM Transactions on Networking 28.4 (2020): 1477-1490.
- Y. Lin, T. He, S. Wang, K. Chan and S. Pasteris, “Looking Glass of NFV: Inferring the Structure and State of NFV Network from External Observations,” IEEE INFOCOM 2019 - IEEE Conference on Computer Communications, 2019, pp. 1774-1782, doi: 10.1109/INFOCOM.2019.8737393.
- Lin, Yilei, et al. “Waypoint-based topology inference.” ICC 2020-2020 IEEE International Conference on Communications (ICC). IEEE, 2020.
- Lin, Yilei, et al. “Multicast-based weight inference in general network topologies.” ICC 2019-2019 IEEE International Conference on Communications (ICC). IEEE, 2019.
Organisations
PSU, IBM US, ARL, UCL